Generations ago, citizens eagerly stood ready across colonial America to defend their families, communities, and interests at a minute’s notice. These first responders, acting in a collective but distributed manner, were referred to as Minutemen. During the American Revolution, they formed collaborative swarms to challenge the overwhelming might of the British Army, and in some instances the Minutemen augmented the Continental Army. Indeed, the name gained such reputation that two centuries later, during the Cold War, the intercontinental ballistic missile system to protect the United States from the threat of Soviet missiles bore the name Minuteman.
The United States is barraged daily in cyberspace by malicious actors. Threats emanate from complex and large state actors with a bevy of sophisticated cyber teams and resources, from advanced persistent threat teams–like the Chinese military Unit 61398– to opportunistic criminal elements and hackers. As more Americans become susceptible to cyber-attacks, hacks, and ransomware such as the Colonial Pipeline incident, which targeted vital infrastructure, or the Equifax data breach of over 140 million people’s accounts, why doesn’t the United States leverage a more whole-of-society approach to cybersecurity? Besides, most of the American cyber ecosystem remains privately owned and operated by either citizens or private entities. And why can’t cyber resiliency and, potentially response, be distributed amongst America’s citizens, marshaling the resources and ingenuity of the third most populous country in the world?
Unfortunately, there are significant hurdles for Americans to be able to respond and strengthen cybersecurity. First, many cyber actions or attacks are too minor, or not the responsibility or priority of government jurisdiction, to elicit a U.S. government response. Second, the U.S. government’s ability to respond is divided into a byzantine maze of conflicting regulations, authorities, and organizations, which include the Federal Bureau of Investigation, the Department of Homeland Security (DHS), U.S. Cyber Command (USCYBERCOM), the Department of State, and others, as well as state and local entities. Third, access to comprehensive cyber resources have and will likely remain beyond the reach of many individuals and small companies, because they are scarce, overly complex, and often prohibitively expensive. Fourth, basic training in cyber hygiene and best practices is lacking for the general public. Finally, most things ‘cyber’ remain poorly understood, a ‘black box,’ for most people.
A reasonable solution is to make cybersecurity more available and approachable. Regrettably, most Americans can only access off-the-shelf commercially available cybersecurity products that have limited capabilities or functionality. As the United States propels itself into new paradigms of 5G, the internet-of-things (IoT), and ubiquitous smart devices, digital creep will continue to infuse all segments of American society, resulting in a drastic and continuing increase in the number of available attack vectors and vulnerabilities. As this future rapidly unfolds, it begs the question of what is the right balance between a public and private response – where are today’s digital Minutemen?
Vast resources continue to be spent on less-than-optimal cyber defenses while the United States continues to rely on the same cyber deterrence concepts. On the contrary, a novel response is to distribute cybersecurity and resiliency at scale and among the American people through a broad and inclusive public-private auxiliary or militia force – the Byteforce.
Accelerating Speed and Scale of Cyber Attacks
American society is careening ever closer to the next cyber crisis point. Once again, cyber resiliency will be pushed to the limit. And there remain serious questions for the cyber domain.
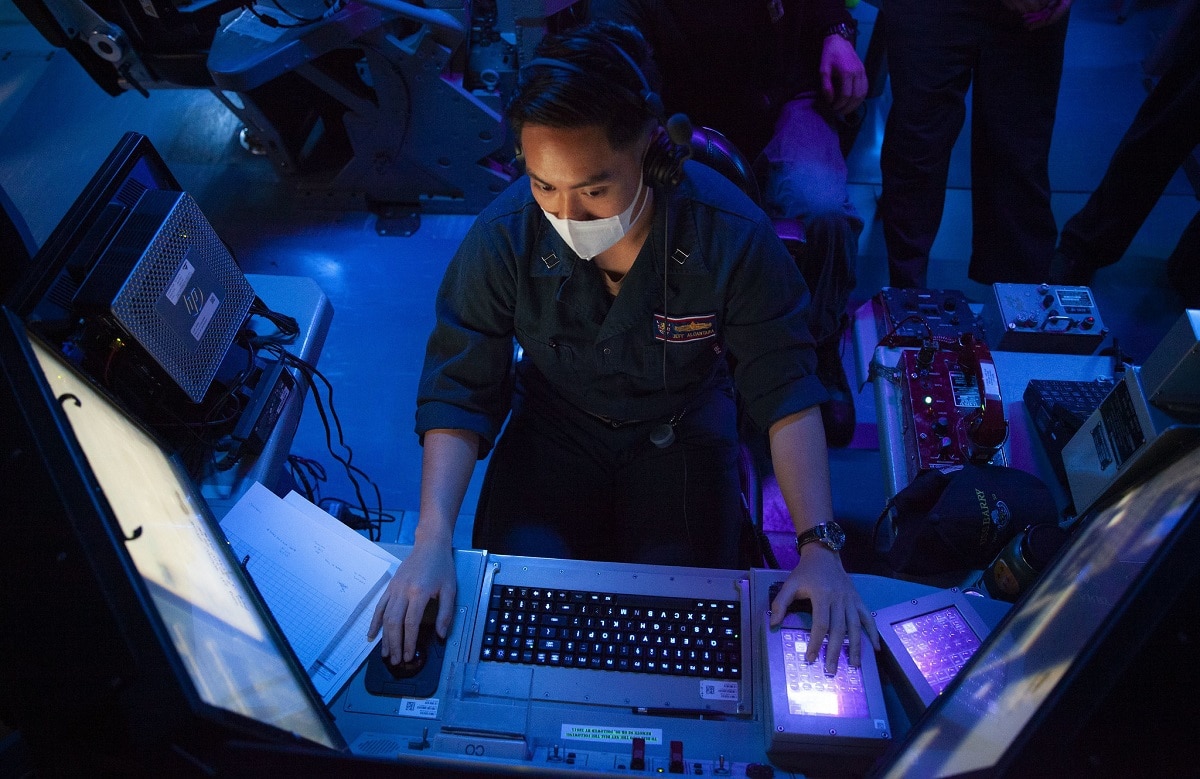
At the moment, all things cyber-security seem to be concentrated in the most tech-savvy clusters of a few regional enclaves or in classified operation centers in places like the National Security Agency (NSA) or USCYBERCOM. Indeed, the Cyberspace Solarium Commission developed a strategic approach for how to defend the United States in cyberspace. But its recommendations stayed predominantly at the public and private-sector higher levels and focus on a limited number of technologists. While the Commission’s other proposals like the establishing a CyberCorp to advance cyber training and expanding the military and federal government cyber workforce are important; rather, the Commission missed opportunities to suggest potential cybersecurity approaches and solutions at the level of the ordinary private citizen. And Byteforce is grander in scale than current volunteer communities of virtuous cyber operators like the Cyber Threat Intelligence League.
With the recent incidents of the SolarWinds and Microsoft365 server hacks, now is the time for America to reimagine approaches to the cyber battlefield and those that operate on it. These cyberattacks continue to affect all levels of American society, not just government officials, corporations, and national infrastructure. The cybersecurity of Americans and American society is a shared national security interest.
Today, there are exceedingly few opportunities for digital patriots to act and enhance America’s cyber frontiers, as the Minutemen did for the American frontiers of yesteryear. The Cyberspace Solarium Commission‘s eighty plus recommendations are a high-profile example of the necessary and continued focus on whole-of-government recommendations. Meanwhile, some American politicians frequently admonish Americans to “learn to code” in order to gain new skills and remain competitive in the transition to the 4th Industrial Revolution which will propel automation and the IoT. Despite much repetition, this political sloganeering has failed to materialize substantial results for Americans. Simultaneously, the demand for cybersecurity talent has only grown in recent years in both the public and private sectors as more than half a million cybersecurity jobs remain unfilled, and calls continue to increase for high-tech immigration and enhanced STEM education pipelines for Americans
Instead, American policymakers should reimagine the existing rules for cyberspace, to empower and even incentivize Americans at all levels to enhance American cybersecurity and resiliency. Americans are more at risk now than ever before in the digital domain. There does exist a largely underserved but engaged citizenry. It is possible to deploy cybersecurity in a more risk-aware rather than a risk-averse fashion. One approach for the United States to empower its digital citizens would be to stand up a cyber cyber auxiliary or militia force for the 21st century, from across the large numbers of ordinary Americans who are ready and willing to do something – the Byteforce.
The Byteforce Construct
One of the most profound outcomes from the GameStop stock incident in January 2021 was the clear demonstration of the power of large, distributed groups of individuals to rally at scale and take collective action for a common cause. Reddit members collaborating in the #WallStreetBets forum conducted a distributed but coordinated action in the stock market against short sellers, thereby saving the company from financial ruin.
Imagine if large numbers of average American citizens, along with their smart devices, were empowered and incentivized to achieve the same against cyber criminals and hackers. But this time on behalf of broader American national security goals and objectives. China leverages its 50 Cent Army of internet trolls to promote Chinese interests and to attack opposing interests, while Russia uses the Internet Research Agency among others. What if Americans on Main Street were empowered, informed, and incentivized to carry out cyber operations at various levels of complexity in defense of America?
Byteforce is envisioned as a public-private partnership, akin to the Civil Air Patrol. In this case, Byteforce can reside under several U.S. government entities, depending on the effects, missions, or actions required. One option would be within the DHS’s Cybersecurity & Infrastructure Security Agency to help protect critical infrastructure. Another option might be for select and screened members of Byteforce to collaborate under the auspices of the military under USCYBERCOM or the NSA as the National Guard could or military reserve units do. In that case, Byteforce may take on a more military-civilian construct with possibly some offensive capabilities so that it can “defend forward” and maintain “persistent engagement.” Maybe some in Byteforce could be allowed to hack-back, under certain conditions. Byteforce could even augment existing U.S. military reserve or National Guard cyber units as necessary. Individual states, like California, New York, or Texas, could even stand-up and regulate their own Byteforce militias.
The Byteforce construct is built upon the importance of a grassroots and an all-hands-on-deck approach to the cyber domain from across American society – at all levels. In this regard, Byteforce is meant to be more inclusive and broader than other proposals like the Cybersecurity Civilian Corps, Digital Corps, or others ideas at the heart of Civilian Cyber Security Reserve Act currently circulating in Congress. These other concepts leverage existing cyber talent or technologists – they are not inclusive and broad enough for all Americans to get involved. Besides, there is no reason why Byteforce could not work in tandem with these other proposed cyber forces.
But to achieve a more inclusive cyber community, initial entry to Byteforce would be open to all U.S. citizens. Access to various Byteforce capabilities or opportunities could be tiered or ‘unlocked’ based on cyber expertise, security background or eligibility, and other criteria, such as experience or certifications. As operations take place, Byteforce could even be incentivized with pay, promotions, or other positive inducements.
Unique Cybertools & Authorities for Byteforce
With such a broad membership pool, Byteforce will have a variety of cyber tools at its disposal for its members. For example, Byteforce members may use customized distributed applications, such as a downloadable app to their computers, smart devices, or other IoT enabled devices. This app will allow Byteforce members to conduct operations or have their processing power leveraged by authorized American cyber operators, similar to the way cryptocurrency rigs constantly mine for digital coins. In this way, Byteforce apps could be harnessed at scale and for larger effects, but all under the coordination and authority of higher cyber officials. In a sense, this ‘game-ification’ aspect of Byteforce capability leverages familiarity with popular and distributed Massive Multiplayer Online Games or MMOGs.
Depending on how Byteforce is constituted, there may be options for members to “unlock” new capability features, promote in rank or status, or pursue different mission objectives, similar to video game approaches, based on a member’s achievement level or contribution. Byteforce may even serve as a means to identify and recruit promising cyber talent for future education, training, government service, or other opportunities. The Byteforce and its app even could be set-up to include critical cyber awareness guides or teaching lessons on various cyber topics.
Other unique options that have been proposed could include the issue of digital letters of marque to the Byteforce, with bounties for successful operations against malign non-state cyber actors, like criminal organizations. The Byteforce can also be used as entry level white hat testers with bug bounties to enhance resilience and shore up American digital defenses across society. Meanwhile, existing authorities and laws should be reconsidered. One idea is to revisit and modify the Computer Fraud and Abuse Act to allow the Byteforce, under proper authorities and national security supervision, to conduct hack-back operations against verified non-state cyber actors. Another idea is for Congress to consider allowing Byteforce members to be ‘deputized’ in contingent circumstances.
Byteforce.exe
Reforming national cyber capacity and resilience is needed now. Using an auxiliary or militia approach will bring the American patriotic ethos of can-do attitudes, creativity, ingenuity, self-reliance, and community engagement to the virtual frontiers of the 21st century. In the absence of an adequate number of cyber personnel, technologists, or other capabilities that can muster cyber security forces quickly, Byteforce may create the scale and speed that the United States requires.
To be clear, Byteforce is not intentioned to put the most complex and sensitive cyber tools or authorities in the hands of laypersons. Moreover, it is not meant to be a cyber vigilante force that roams the digital landscape without direction. On the contrary, it is meant to democratize cyber resiliency and knowledge to American citizens, helping to defend themselves, act in the national interest, enhance deterrence, and focus precious resources on high-end cyber threats.
Byteforce can accomplish many positive outcomes. It can engage the American citizenry, build the national cyber talent pool, put Americans to work, create a formidable cyber force for deterrence and targeted cyber operations (when needed), and foster an esprit de-corps against cyber adversaries and criminals attempting to do America harm.
Byteforce harkens back to a constructive, public-private response in American history. At its most fundamental level, the United States government has been inadequately able to respond, at scale, in the cyber domain to protect both American citizens and society. Given the growing need to protect American cyberspace, America should rediscover its heritage of the Minuteman and establish a Byteforce to engage and defend on the frontiers of cyberspace.
Wilson VornDick, a 1945 Contributing Editor, is a RANE Network Analyst, DUCO Expert, and China Aerospace Studies Institute Associate. He is also an officer in the U.S. Navy Reserve. The views expressed here are his own.