Coming Soon: a US-Russia Cyber War? – The United States and Russia may not be fighting a ground war, but a war in cyberspace is certainly being waged. On Monday, the White House issued a new warning about the potential for Russia to engage in malicious cyber activity against the United States in response to the unprecedented economic sanctions that were imposed on Moscow following its unprovoked invasion of Ukraine.
The Biden Administration also warned that there is now developing intelligence that Russia may be exploring options for potential cyberattacks.
“Timely message – not only has Russia warned of attacks on western infrastructure – there has been evidence of the change of hacks from purely financial, e.g. in the case of Colonial Pipeline, for ransomware to more malicious instructions and efforts to disrupt western critical infrastructure,” said Garret Grajek, CEO of cybersecurity software firm YouAttest.
“The alert is warranted and should extend to all Internet-facing systems that were identified in all the 16 categories of infrastructure identified by the U.S. CISA (Cybersecurity & Infrastructure Security Agency) in PPD-21 (Presidential Policy Directive 21),” Grajek said via an email to 19FortyFive. “The key to securing these systems is to be aware of all the assets, especially identity, and then changes in roles and permissions – since controlling of admin accounts is crucial to the lateral movement, persistence and data exfiltration that the hackers desire to implement.”
Steps to Take
The White House has also urged American companies to execute a number of steps to ensure that they are protected in the event of an attack.
Among the key suggestions pushed forward were to mandate the use of multi-factor authentication on computer systems to make it harder for attackers to get onto a system; deploy modern security tools on computers and devices to continuously look for and mitigate threats; and to check with cybersecurity professionals to make sure that these systems are patched and protected against all known vulnerabilities, and change passwords across networks so that previously stolen credentials are useless to malicious actors.
Every American is reminded to back up their data and ensure they have offline backups beyond the reach of malicious actors and run exercises and drill your emergency plans so that you are prepared to respond quickly to minimize the impact of any attack.
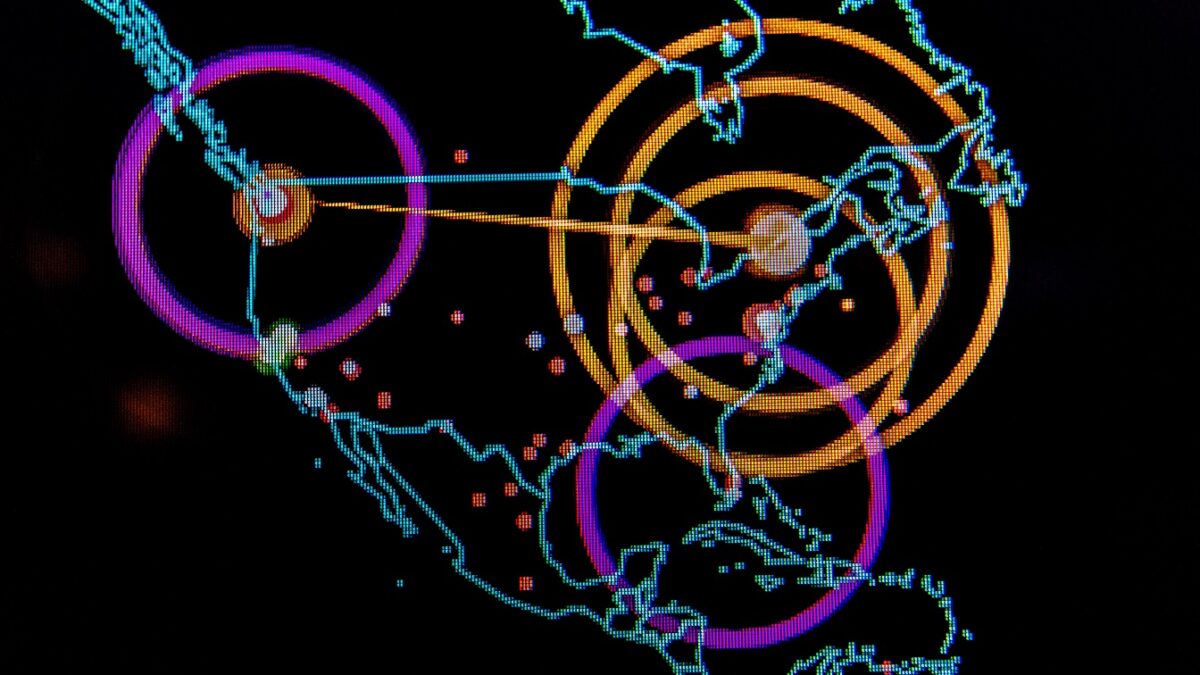
The Norse data wall on the operations floor of the 275th Cyber Operations Squadron, called the Hunter’s Den, provides real-time worldwide cyberattack sources and attack locations for the 175th Cyberspace Operations Group of the Maryland Air National Guard at Warfield Air National Guard Base, Middle River, Md., Dec. 2, 2017. This portion of the screen is focused on attacks within North America. (U.S. Air Force photo by J.M. Eddins Jr.)
Data should be encrypted so that it cannot be used if it is stolen. In addition, as humans remain the weakest link in cybersecurity, the White House called upon greater efforts to educate employees to common tactics that attackers will use over email or through websites, and encourage everyone to report if their computers or phones have shown unusual behavior, such as unusual crashes or operating very slowly.
“There are several reasons to pay attention to these messages,” explained Purandar Das, co-founder and the CEO of encryption-based data security solutions company Sotero.
“Almost everybody has been saying and seeing an increase in cyber-attacks,” Das said via an email to 19FortyFive. “Simply put, cybercrime pays, and it has attracted and will continue attract talent individuals that see it as a path to making money.”
It is also a confusing time that involves two nations that have historically possessed and demonstrated very good skills in the cyber security and cybercrime areas, added Das.
“Countries under duress have and will utilize cyber-attacks as a way to retaliate and to get around sanctions,” Das continued. “The U.S. being the face of such sanctions and a history of poorly protected infrastructure make it a tempting target. Add all this together and the warnings make a lot of sense.”
Is it Enough?
While every computer user should maintain his/her vigilance, these efforts could still fall short if Russia – or another state actor – were to engage in a full-blown cyberattack.
“Russia and other nation-state actors have a vast amount of computing resources as well as well-coordinated teams to play a long game against targeted Western governments, enterprises and MNCs (multi-national corporations),” warned Rajiv Pimplaskar, CEO of VPN (a virtual private network) provider Dispersive Holdings, Inc.
“That motivation in such situations is not just economical but also strategic means sensitive data that is detected can be used to reverse engineer source and destination relationships as well as identify flows of interest,” said Pimplaskar. “Furthermore, nation-state toolkits can use public cloud as a gateway to get underneath the encryption layer and capture the data flow itself for future analysis.”
Even still, some of the cybersecurity methods that the White House has called for in recent months – notably zero trust – could fall short.
“Traditional zero trust approaches stop at the network and are largely ineffective against nation-state actors,” suggested Pimplaskar. “Critical infrastructure companies should bolster their cyber defense posture with advanced communications security that can obfuscate resources, as well as leverage data multipathing to present a harder target for such threat actors.”
Now a Senior Editor for 1945, Peter Suciu is a Michigan-based writer who has contributed to more than four dozen magazines, newspapers and websites. He regularly writes about military hardware, and is the author of several books on military headgear including A Gallery of Military Headdress, which is available on Amazon.com. Peter is also a Contributing Writer for Forbes.

