The B-21 Will Control Drones From the Cockpit, Relay Satellite Data to Ground Forces, and Add Weapons That Don’t Exist Yet – “Open Architecture” is a phrase used throughout Pentagon weapons development for decades, referring to a technical set of standards or infrastructure intended to enable persistent, long-term modernization.
The core concept is clear and often cited, as it involves engineering IP protocols and interfaces to maximize interoperability and ensure that upgrades, such as new weapons and sensors, can be added without requiring hardware reconstruction.
Perhaps a new weapon emerges and needs to be integrated into the B-21 Raider?
The idea is to build the platform from its inception with an integrated capability to quickly accommodate new technologies as they emerge.
Common Standards and the B-21 Raider Bomber: The Real Secret Weapon
Years ago, when senior Air Force scientists and weapons developers were performing early conceptual work on the B-21 and beginning to manufacture and design some subcomponents, former Gen. Arnold Bunch (formerly commanded Air Force Materiel Command) told 19FortyFive the service was prioritizing open architecture for the B-21 Raider to ensure the next-generation stealth bomber remains “in front” of rival platforms in future years.
With common standards, in which IP Protocols are engineered with “1s” and “0s” to integrate with new systems, an existing platform, such as the B-21, can add, integrate, or accommodate new weapons, computing, avionics, or sensors.
Rapid modernization and ubiquitous interoperability, supported by new generations of network security technology, is the essence of the intent with open architecture.
The concept of open architecture is extremely significant for the B-21, given its expanding mission scope and the pace of technological change.

B-21 Raider Bomber. Artist Rendition/Creative Commons.

B-21 Raider. Image Credit: Creative Commons.
New algorithms will help perform analytics on vast amounts of incoming sensor data to identify relevant moments, solve problems, organize information, and perform collective analysis across pools or integrated data arriving through otherwise incompatible transport-layer communication technologies.
Multi-Mission Bomber
This is critical to the B-21, given the expectation that rapid technological change will continuously offer new combat capabilities and a high tactical relevance to the B-21’s mission scope.
The Raider will not only operate as a high-altitude precision bomber with new generations of stealth technology, but will also control drones from the cockpit and serve as a flying aerial node or command-and-control hub.
Networking technology has advanced to the point where air, land, and sea manned and unmanned nodes can increasingly share processed, high-value data in seconds, enabling forces to quickly verify and destroy targets, send time-sensitive intelligence across a joint force, and operate at new levels of manned-unmanned teaming.

B-21 Raider Bomber.
For instance, a B-21 will be positioned to receive information from satellites, ground forces on the move, unmanned systems, and fixed-wing aircraft, enabling the bomber to collect data, perform analytics, and transmit organized, critical information across multiple domains in near real-time.
It is often referred to as collective AI ‘at the edge’, meaning command and control technologies will gather, organize, analyze, and transmit vast volumes of data in milliseconds. This offers human commanders a clearer window into making critical combat decisions.
Streamlining and expanding interoperability between host platforms and emerging systems yields unparalleled advantages in sustainment and modernization.
Yet greater connectivity between large weapons systems and their subcomponents can also increase vulnerability by creating more points of entry for a potential intruder.
Additionally, if a cyber-intruder penetrates a node or element of a platform, large areas of a multi-node network could become vulnerable or even compromised.
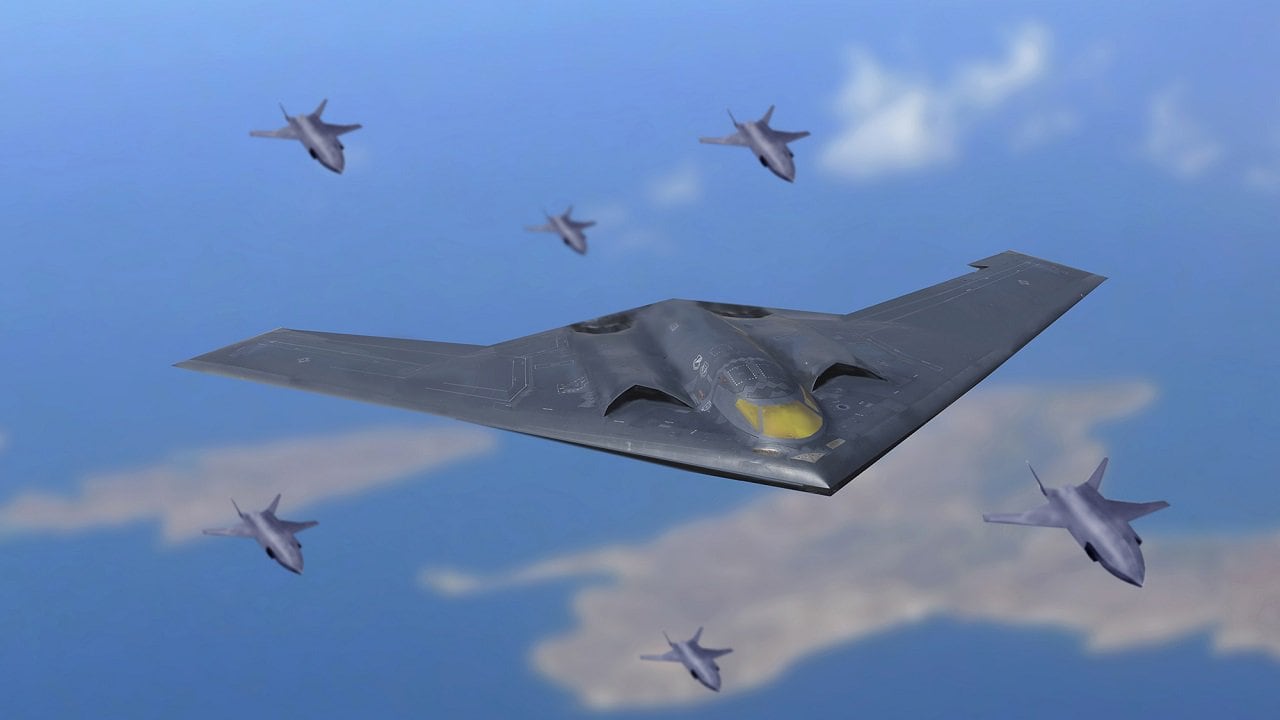
An artist illustration depicts a U.S. Air Force extended-range B-21 Raider escorted on a mission by armed unmanned next generation air dominance platforms. This fictional bomber features longer, wider wings, and a deeper fuselage that accommodates larger fuel tanks and dual weapons bays that enables the bomber to carry a much larger and varied payload. Mike Tsukamoto/staff; Greg Davis/USAF
Therefore, Air Force weapons developers are implementing new methods to harden and secure data networks against intruders.
The idea is to “bake in” cyber resilience early in the developmental process so vulnerabilities can be identified and corrected during the early phases of a weapons system.
About the Author: Kris Osborn
Kris Osborn is the President of Warrior Maven – Center for Military Modernization. Osborn previously served at the Pentagon as a highly qualified expert in the Office of the Assistant Secretary of the Army—Acquisition, Logistics & Technology. Osborn has also worked as an anchor and on-air military specialist at national TV networks. He has appeared as a guest military expert on Fox News, MSNBC, The Military Channel, and The History Channel. He also has a Masters Degree in Comparative Literature from Columbia University.

